 But it doesn’t matter how long and complex a password is if the user is on a personal (read: unsecured) device connected to a home network (also probably unsecured). Random guesses by a computer program won’t be necessary because hackers will be able to read the password in plain text.
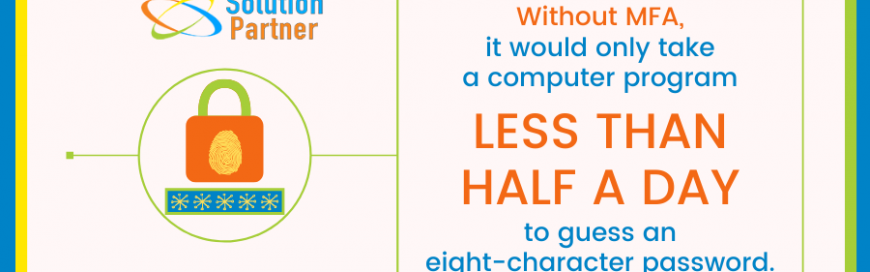
Unless you add multifactor authentication into the mix.
But it doesn’t matter how long and complex a password is if the user is on a personal (read: unsecured) device connected to a home network (also probably unsecured). Random guesses by a computer program won’t be necessary because hackers will be able to read the password in plain text.
Unless you add multifactor authentication into the mix.
What is multifactor authentication?
All multifactor authentication (MFA) does is add a second step to login processes (sometimes a third and fourth as well). Think of it as a gate with multiple padlocks, one for each step of the login process. If a hacker knows your password, MFA means they still have another obstacle to overcome — the second padlock. Instead of just requiring another string of characters, MFA asks for a different type of information in step two. A password is something you know, so we recommend adding one of these identifiers to shake things up:- Something you have – Common examples of this include codes sent to physical objects that only the account owner should possess, such as a mobile phone or physical security token.
- Something you are – Verifying a user’s identity based on biometric information like a fingerprint or facial scan is arguably the best way to stop unauthorized access to an account.
MFA also makes logging in to apps easier
Without MFA enabled, employees must create new and complex passwords every few months to avoid a data breach. That annoying policy practically forces an employee to guess their own password since they haven’t used the same one long enough for it to lodge itself in their memory. With MFA enabled, there’s no need to constantly change passwords. There’s also an AI component to MFA that further simplifies security. For example, if a user logs on at the same time from the same device every day, they would only need one authentication method, such as a fingerprint scan on their mobile phone.Is MFA required by HIPAA?
MFA is not explicitly required by the Health Insurance Portability and Accountability Act (HIPAA). However, implementing it does cross off some of the Administrative Safeguards requirements. If you operate in the healthcare industry and choose to optimize for single-factor authentication, you subject yourself to several vague regulatory requirements, such as having:- “Appropriate administrative, technical, and physical safeguards to protect the privacy of protected health information.”
- “Procedures for creating, changing, and safeguarding passwords.”
- “Procedures to determine that the access of a workforce member to electronic protected health information is appropriate.”
What is Security-as-a-Service (SECaaS)?
Security-as-a-Service (SECaaS) consolidates MFA, firewall management, email security, and anti-malware software into a single package for a flat monthly rate. It kicks off with a network assessment to uncover which solutions you need to protect your data and customer relationships, without adding complicated IT requirements to you or your team. Every business has unique technology needs. Our SECaaS might be the answer for some while others can get by fine with a smaller-scale solution, which we can also provide. Contact us today if you’re interested in a quote for our cybersecurity services.Unsure how to protect your business
Maybe it's time for a technology partner. Enter your name and email address on the respective fields on the right to receive our free eBook, Managed Services: Why they're perfect for your SMB

Leave a comment!